On your Linux server, in a Terminal window, execute these commands:
mkdir -p work/src/my_project/caesar1
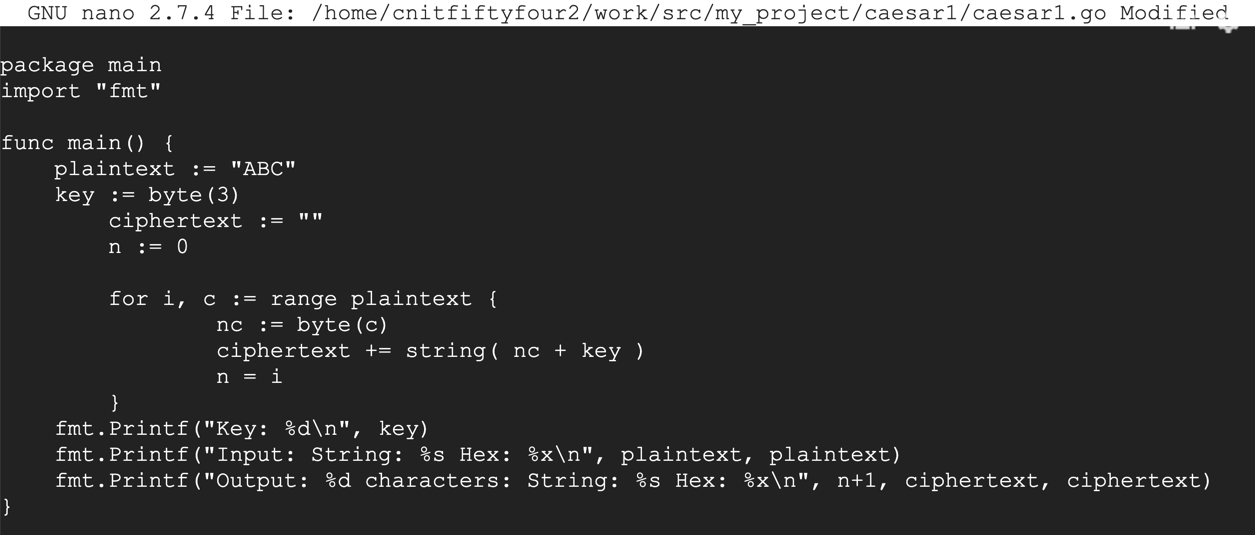
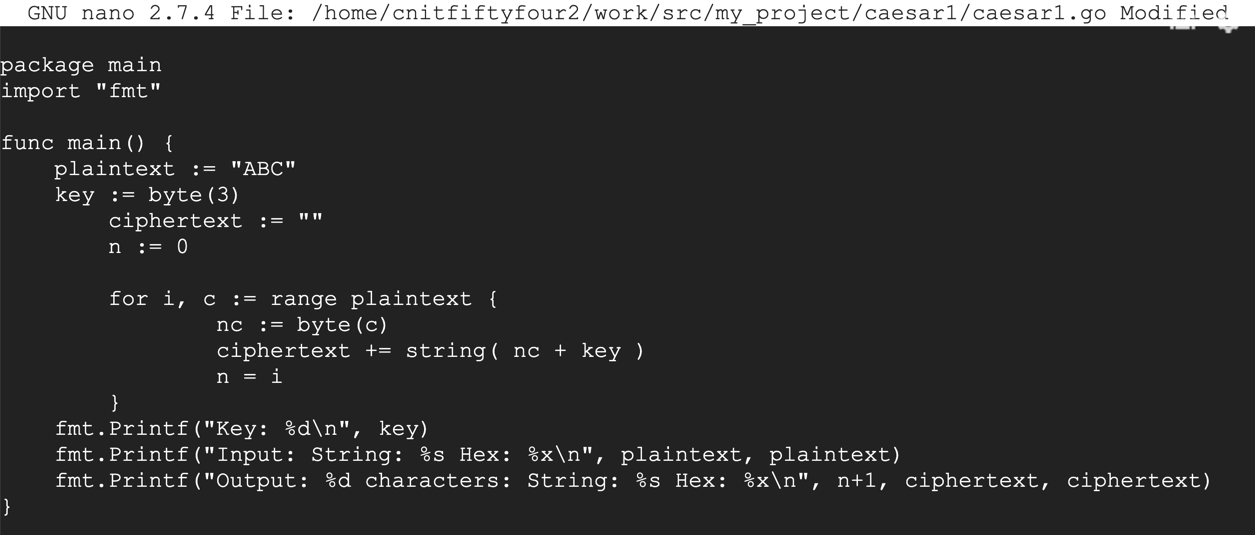
nano ~/work/src/my_project/caesar1/caesar1.go
package main
import "fmt"
func main() {
plaintext := "ABC"
key := byte(3)
ciphertext := ""
n := 0
for i, c := range plaintext {
nc := byte(c)
ciphertext += string( nc + key )
n = i
}
fmt.Printf("Key: %d\n", key)
fmt.Printf("Input: String: %s Hex: %x\n", plaintext, plaintext)
fmt.Printf("Output: %d characters: String: %s Hex: %x\n", n+1, ciphertext, ciphertext)
}
Save the file with Ctrl+X, Y, Enter.
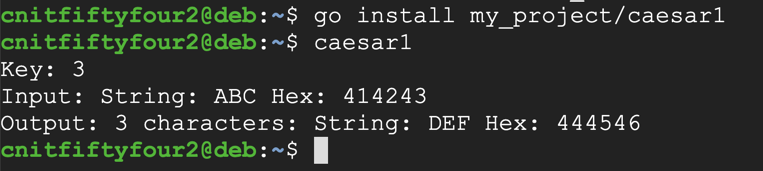
Execute these commands to compile the program and run it:
go install my_project/caesar1
caesar1
ALICEThe flag is the ciphertext as a five-letter string, like ABCDE
UKORNGIt was encrypted with a key of 2.
The flag is the plaintext as a six-letter string, like ABCDEF
ZNK&LRGM&OY&IXGIQKXNote that this is a Caesar cipher based on ASCII codes, so shifting Z by one does not result in A, but in [
0f333e7b3d373a3c7b32287b696e6d04101e0208The key is a byte, between 0 and 255.
echo -n ABC >infile
mkdir -p work/src/my_project/file1
nano ~/work/src/my_project/file1/file1.go
package main
import ( "fmt"; "io/ioutil" )
func main() {
dat, err := ioutil.ReadFile("infile")
if err != nil { fmt.Println("Read Error: ", err) }
size := len(dat)
fmt.Println("Read in: ", size, " bytes")
err = ioutil.WriteFile("outfile", dat, 0644)
if err != nil { fmt.Println("Write Error: ", err) }
}
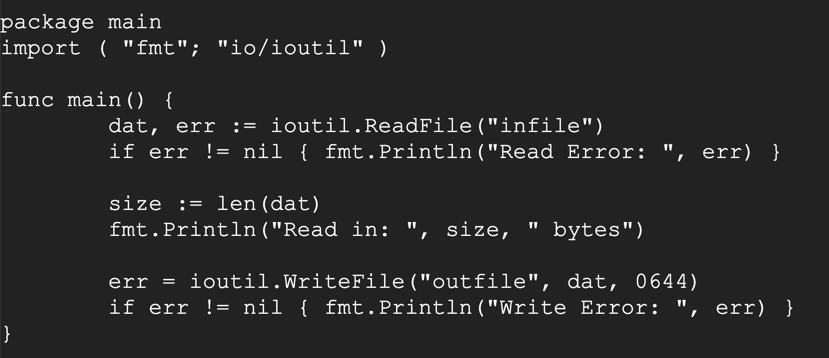
Save the file with Ctrl+X, Y, Enter.
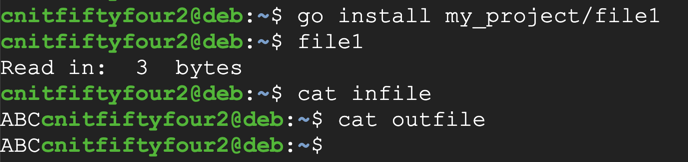
Execute these commands to compile the program, run it, and examine the results:
go install my_project/file1
file1
cat infile
cat outfile
mkdir -p work/src/my_project/file2
nano ~/work/src/my_project/file2/file2.go
package main
import ( "fmt"; "io/ioutil" )
func main() {
dat, err := ioutil.ReadFile("infile")
if err != nil { fmt.Println("Read Error: ", err) }
size := len(dat)
fmt.Println("Read in: ", size, " bytes")
out := make([]byte, size)
key := byte(3)
b := byte(0)
for i, c := range dat {
b = byte(c)
out[i] = b + key
}
err = ioutil.WriteFile("outfile2", out, 0644)
if err != nil { fmt.Println("Write Error: ", err) }
}
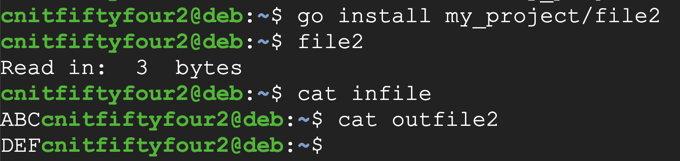
Execute these commands to compile the program, run it, and examine the results:
go install my_project/file2
file2
cat infile
cat outfile2
wget https://bowneconsultingcontent.com/pub/Attack/proj/A54.4_infile
wget https://bowneconsultingcontent.com/pub/Attack/proj/A54.5_infile
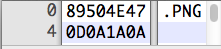
Notice that the first 4 bytes are 89, 50, 4E, 47; the 2nd through 4th byte spell out PNG in ASCII.
Decrypt the file. When you get it, change its filename extension to PNG and open it in an image viewer or Web browser.
The flag is visible in the image.
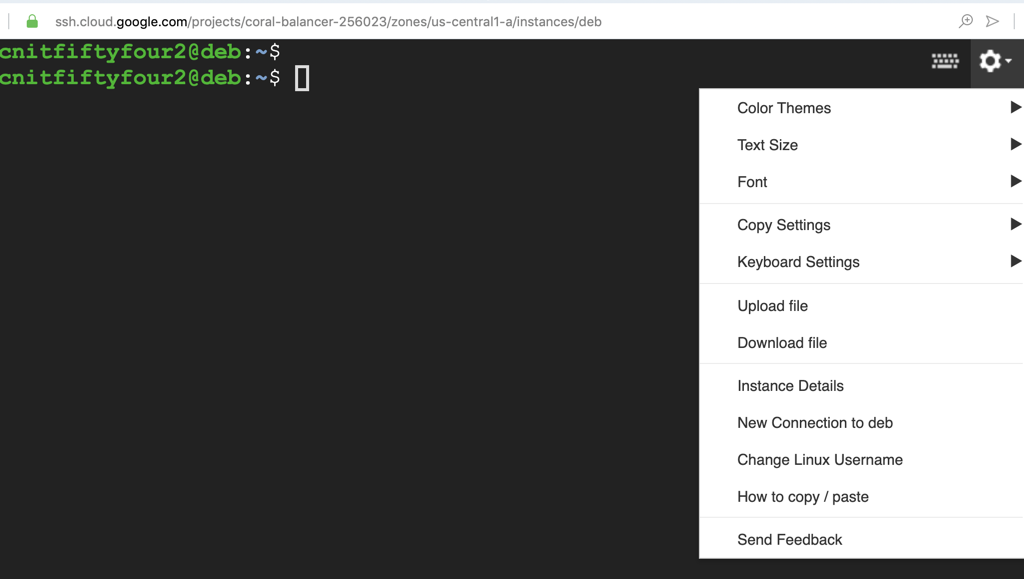
To download a file from a Google cloud server, click the gear at the top right, as shown below.