This is such a serious security flaw that the FTC punished Fandango and Credit Karma for doing the same thing in 2014.
If your host machine uses Mac or Linux, use Genymotion.
If your host system runs Windows, use Burp and Nox.
Then drag the round button up from the bottom center of the home page, click the "Harvard" icon, and grant it the permissions it needs.
This worked with my Android 11 emulator on Sept 12, 2022, using Android Studio.
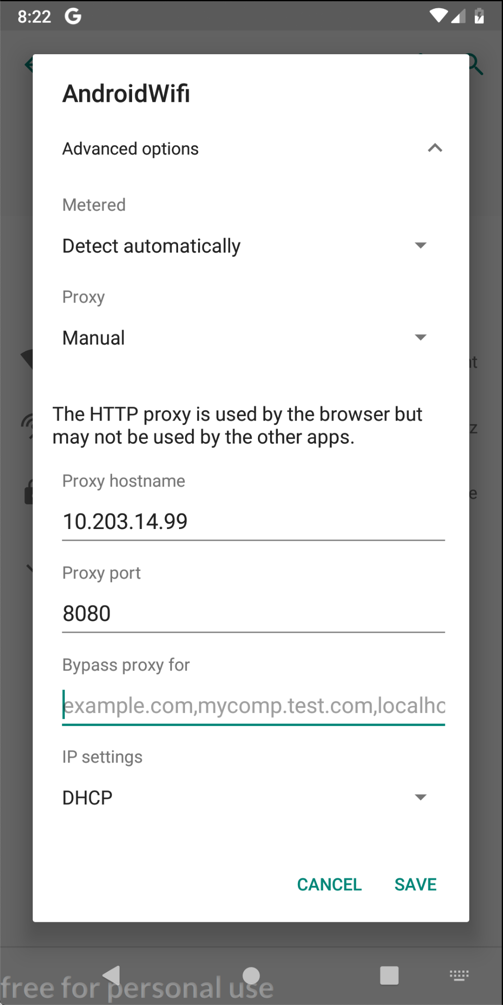
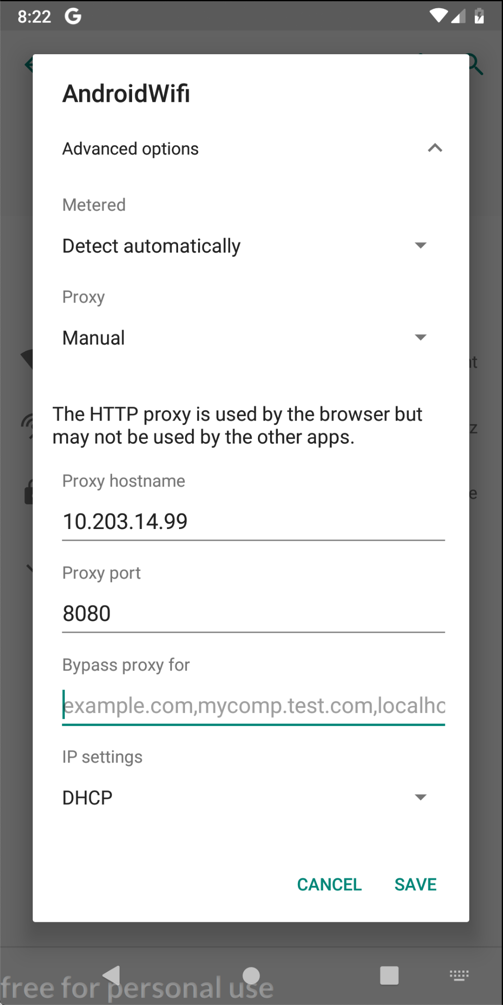
On your Android device, click SAVE.
At the bottom center of the device, click the round Home button.
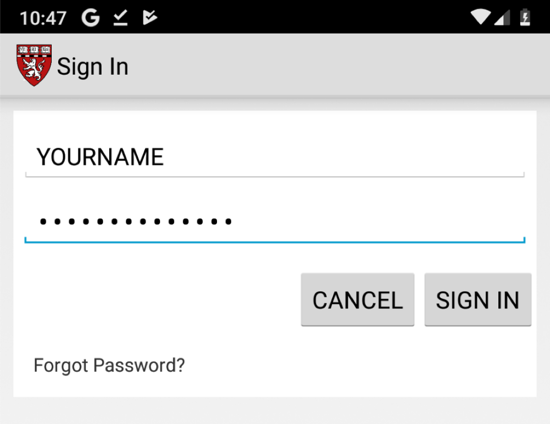
Click "Sign in" and enter test credentials, as shown below.
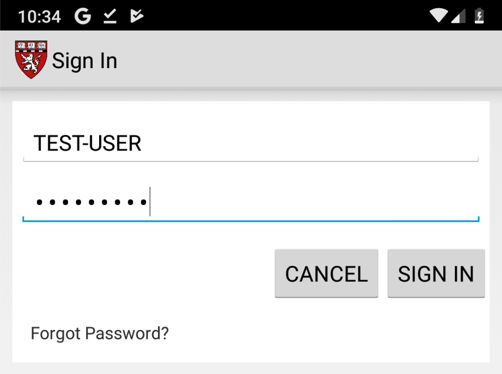
Click "SIGN IN".
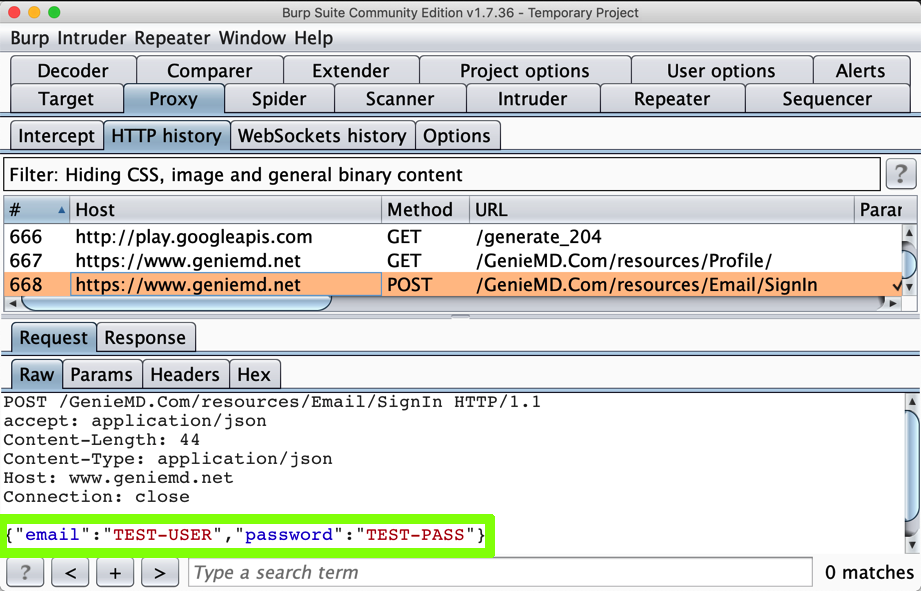
In Burp, on the Proxy tab, click the "HTTP Requests" sub-tab.
Find the POST method going to /GenieMD.Com/resources/Email/SignIn.
The username and password appear in Burp, as shown below:
If you have been doing these projects in order, and you are using a Mac, this is not a security problem, because you have the PortSwigger certificate installed--your Android device has been told to trust Burp.
In Burp, on the Proxy tab, on the "HTTP history" sub-tab, right-click any entry and click "Clear history". Click Yes.
Click OK.
You should see an error message, as shown below.
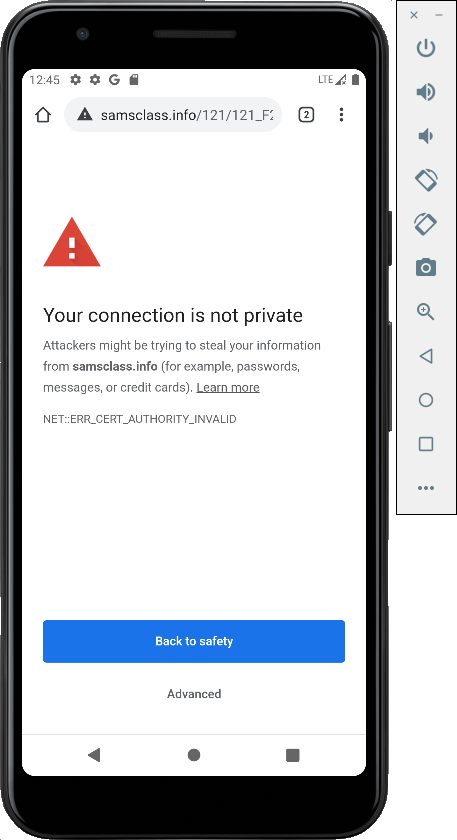
No valid HTTPS connections can be made from your device now, because it no longer trusts Burp.
Using the Android Studio Emulator
My Android 11 emulator refused to send any HTTPS traffic to the Burp proxy. To fix that problem, in Settings, remove the proxy settings.Then close Android Studio and the emulator and execute this command from a Terminal:
(The path is for a Mac; on a Windows machine the path will be something like C:\Users\{User}\AppData\Local\Android\Sdk\emulator\emulator )
You see a list of your available emulators, as shown below.
Execute this command to start your emulator with a http-proxy, using the correct name for your emulator and changing the IP address to the listening address you set in Burp:
This should redirect HTTP and HTTPS traffic to the proxy.
Click "Sign in" and enter test credentials, including your name, as shown below.
Find the POST method going to /GenieMD.Com/resources/Email/SignIn.
The username and password still appear in Burp, as shown below:
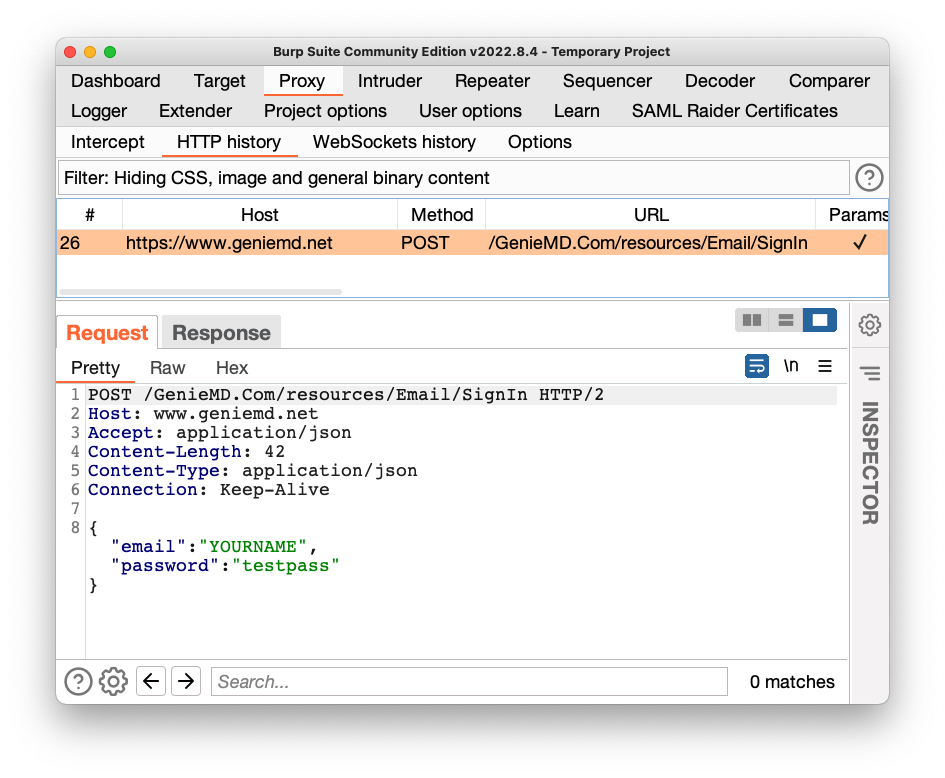
This is a big problem--the MITM attack is allowed. GenieMD exposes its users to this attack, because they don't bother to validate SSL certificates.
M 107.1: Server (15 pts)
In Burp, in the lower pane, click the Response tab.The flag is the text covered by a green box in the image below.
M 107.2: Find the Server (5 pts extra)
Uninstall the original app and install this app instead:Execute a login request. The flag is the domain name of the server it sends a POST request to.
M 107.3: Registration (15 pts extra)
Use the same A31.2.apk app. Launch the app. Click "Join Now".It asks for a registration code, as shown below.
Refer to project M 402 to install jadx-gui, open the APK in that tool, and use the Nagivation, "Text Search" option to search for registration_
Find the registration code. Use it in the app to see the flag, as shown below.
M 107.4: Registration (20 pts extra)
In jadx-gui, expand Resources and look in the META-INF folder.Examine the code-signing certificate for the A31.2.apk app. The company name is in leetspeak. That company name is the flag.
Links to previous setup projects removed 6-1-19
Points labeled "extra" 1-13-2020
Challenge 3 cleaned up and images added 1-24-2020
A31.2 specified for M 107.4
Note re: Android 5 added 1-28-2020
Updated for the Android Studio emulator 9-12-22
Hint added to 107.3 9-19-22
Another hint added to 107.3 2-15-24
107.3 and 107.4 instructions changed to use jadx-gui 9-16-25